Supply Chain Trust Minimized

Just getting a legit Coldcard into your hands is the hard part sometimes—not just with international shipping and customs shenanigans.
Our own paranoia, and independent security researchers, have always been discussing what could happen if a trojan-horse was added in an Coldcard on its way to you.
First things first, it’s always recommended to load the firmware yourself when you receive a new Coldcard. We have never received any report of a real-life supply-chain attack on any of our shipments.
Minimizing Trust: No Official Resellers
You may have noticed we do not have official resellers. Trusting a third party in the supply chain is not encouraged. You should buy from store.coinkite.com or find locals who you know and trust.
Any listing you might find on EBay or Amazon, is not from us, regardless of any branding elements they may be stealing. Sadly such sales must be regarded as traps for the Bitcoin beginner. There is usually nothing we can do to take down these listings, but we do monitor and report them as best we can.
If you are a reseller and you don’t want to get involved in these risks, please consider joining our affiliate program.
Check the Bag, Security Tape and Case Welding
We’ve always shipping the Coldcard in a security bag to mitigate the risk of interception during shipping. If you’ve read our quick-start guide you know that the Coldcard initial setup shows you the “Bag Number” which ties the specific unit to your bag.

As noted sarcastically in our docs: This is merely one of many layers of our security, and we know that plastic bags can be “hacked” with sharp knives and so on.
The red tape should also be inspected. It should look very even, just as smooth as the rest of the plastic. If it is distorted, or gummy, it may have been tampered-with. Opening and closing the bag with a “heat gun” is of course easy, but you will be able to see the tampering.
The good news is we do know that our customers check the bag carefully, because we routinely get false-positive reports from customers on our support system. (Typically it’s been opened by a customs inspector, or a knife went awry during unboxing on receipt.)
We would also encourage customers to look closely at the Coldcard’s plastic case and check the seals around its perimeter. We use ultrasonic welding which fuses the front and back pieces of polycarbonate plastic together. Taking it apart means breaking it.
Freedom To Develop vs. Firmware Jail
From the start, we’ve wanted other devs to be able to contribute to the Coldcard, and so when it came time to completely wall-off our garden, we decided that the Coldcard would still allow execution of code that was signed by a key that is well know. We call this “key zero” and since it’s on Github, any developer can make firmware that the Coldcard will run.
A big scary warning is shown for a full 30 seconds at boot-up when this happens:
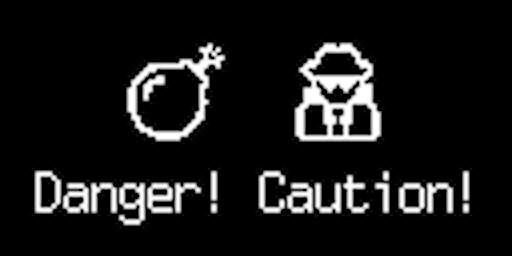
As you can see, it sets a definite mood!
We’ve done this because we didn’t want to close the door to professional and third-party developers creating new things for our platform. Such a developer can take new Coldcard, and put their own firmware on them, and sell them as special-purpose devices, like a password managers or U2F tokens.
Latest Report
Recently a security researcher has reported that he was able to make a Coldcard run new firmware, and appear as a new unit. The ColdCard is designed to offer this functionality, and we documented it two years ago. If the plan is to make a trojan-horse device, an attacker would have to successfully open and then close the bag without damaging it while hoping the user doesn’t upgrade their firmware upon receipt. This is not a practical nor scalable attack.
Please note his proposal only would apply to new units if an attacker were able to intercept the parcel before it arrived to you. If this is part of your threat model, then his attack can be avoided by loading the latest firmware (from our website, preferably verified with GPG).
There is only space for one firmware image on the Coldcard, so the known-good firmware would undo any tampering done, and the upgrade process is accomplished with the unchangeable boot ROM.
We know from experience that our customers nearly always upgrade on receipt anyway. But due to this disclosure, we will be recommending updating to fresh firmware, in the “getting started” docs.
Reality Check
Coldcard has become the industry benchmark for good reasons:
- UN-PWNED: no seed extraction has been demonstrated.
- Bitcoin only
- Open source
- Top-to-bottom physical security
- Intense pace of new features
- Timely security patches
Longer Term
We have been thinking about this from all angles, since Coldcard was born. We have a lot of novel solutions, but some represent privacy risks, involve more cost, or carry other negative consequences.
We are open to suggestions or opinions from the community about options.
1) Bag: We are already improving our security bag. The cost difference is reasonable, and the new one is considered “level four” based on international standards. We will update our docs with new pictures once those are shipping. It’s still a bag though.
2) Jail: We could block firmware running on Coldcard to only binaries that we have built. Experienced Bitcoiners will see this as an inversion of trust: you would be forced to trust Coinkite, which isn’t as good as what we have now, where anyone can build the firmware from source and run it.
3) Tracking (no way): We could track bag numbers, or an additional, longer random identifier, and share that with you over email. We do not link bag numbers with customers (or invoices) at this time. Our thinking is that this is a privacy risk for you, and we’d rather not know the specific unique numbers associated with our customer’s Bitcoin storage devices. We already know what’s down that road: constant subpoenas from law enforcement, every time they investigate someone with a Coldcard.
4) Snap: We have an idea that is better than the secure bag: a snap-off tab that fully blocks the USB port. To load new firmware, or do anything with the Coldcard, you’d have to break it off. This creates some manufacturing challenges, because we like to do final test after the case in welded in place. Our preference is to be able to do that final test just before the “bag number” is assigned and burned-in.
5) Next Gen: Future hardware may already include mitigations that we can’t talk about today. Let’s just say why stop at one secure element?