Coldcard™ Mark 3 Announcement


Pre-Order Now
Batch 1 Mk3, limited quantity
Pre-Sale discount, $20 OFF!
Today we are announcing Coldcard™ Mark3, more security!
What’s New?
This hardware update replaces the chips used for both the secure element and also the main micro. The new ATECC608A secure element is being used to give us a powerful new security model for PIN attempts: the Mk3 will always brick after 13 failed PIN attempts, and that policy is enforced entirely by the secure element and cannot be bypassed by any code in the main micro.
The main micro has been upgraded to give us more memory to enable additional software features in the future. We’ve managed to bump up the memory by 2.5 times while keeping the cost under control. This will allow the Coldcard firmware to sign more complex transactions, and more complex signature types that may be coming in the future.
We’ve also hardened the Coldcard Mk3 against side-channel attacks. In practical terms, this means we are emitting less noise on the USB lines and across the EM spectrum. We already had software mitigations during signing, and when showing seed words. These changes are in hardware and are even better. We don’t know of any practical side-channel attacks at this time, but we wanted to get ahead of the game.
We don’t plan on stopping hardware iteration any time soon! Mk4, Mk5… If you’re bummed that your awesome Coldcard Mk2 is suddenly looking old—we’ve got early-bird pricing for you.
Some of our competitors are funded by scammy shitcoins, but we are pure Bitcoin all the way. So as long as you keep buying, we will keep making firmware upgrades, adding features, and improving our security measures.
Mark2 is still supported in current firmware releases and we will try to support it with updates as long as practical.
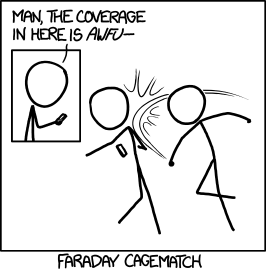
Side-Channel Attack Hardening
Common-mode chokes, ferrite beads, power supply bypassing…
Having the weapons you need to win your faraday cage match: Priceless.
Secure Element Changes
-
Self-bricking after 13 failed PIN attempts: Earlier generations of the Coldcard used the 508A chip, but the new features of the updated 608A is required to make this work securely. (Note: Counter resets after correct PIN entry)
-
The old forced-delay system has been removed, but we warn you lots about the very limited number of PIN attempts you are consuming.
-
Secondary wallet features removed. We could not provide the same level of protection for the secondary wallet compared the primary (due to limitations in the secure element). We recommend BIP39 passphrases instead of this approach.
-
A new “long secret” storage slot is introduced: It can store 416 bytes of binary data in the secure element. We have a project in mind for this very secure data but we can’t talk about that yet. This slot has the same level of protection as the main seed words, but is completely independent of them.
-
The secrets stored in the secure element are now encrypted by a one-time pad held in the main micro. This is a defense against any unknown security issues which compromise the secrets in the 608a and not the main micro itself.
-
PIN values are now stretched using HMAC(SHA256) using secrets known only to the secure element (and unique per device). The KDF (key derivation function) that we are using is documented in a separate python program (see source code
stm32/bootloader/mathcheck.py). -
Successfully using the duress PIN will not cost an attempt on the real PIN. If the duress PIN works, we show zero login failures, but the number of PIN attempts has not actually been changed.
-
Secure element is now lovingly covered by epoxy.
Read more about the technical changes in this whitepaper which has been updated reflect Mk3.
Main Micro Changes
The older Coldcards had 128 KiB of SRAM. The new chip (STM32L496RGT6) has 320 KiB: an increase of 2.5 times. This is the only major difference in the new chip, and it does come at a slight cost increase, as you would expect.
This additional memory will help you sign more complex transactions right now, and we expect future firmware features will make good use of the additional memory.
Future Ideas
- Address explorer (for receiving)
- Shamir secret backup
- Tor remote signing service (HSM mode)
- Hot wallet co-signing firmware
- Message signing using bech32 or p2sh-p2wpkh addresses
- More complex P2SH script support
- Confidential transactions
What is the Coldcard?
What is the Coldcard™? It’s a Bitcoin hardware wallet, so it signs transactions and can be used offline.
-
BIP39 based, which means you can backup the secret words onto paper, and have lots of sub-accounts and unlimited independent payment addresses.
-
It knows how to understand transactions, so you can see what you are approving.
Follow our new Twitter account to keep up-to-date with @COLDCARDwallet
But it’s different!
-
NO specialized software required. No USB connection required: put your PSBT (partially signed Bitcoin transaction) file onto a MicroSD card, and insert to sign.
-
It’s cheap! Simple packaging, plain design, no fancy boxes, no redundant cables.
-
It’s ultrasecure! Real crypto security chip. Your private key is stored in a dedicated security chip, not the main micro’s flash.
-
Easy back-up! MicroSD card slot for backup and data storage. This allows truly offline signing, by transferring the unsigned/signed transactions on sneakernet.
-
Open source software design runs Micropython and you can change it.
Other features:
-
Full-sized numeric keypad makes entering PIN easy and quick.
-
Larger 128x64 OLED screen.
-
Participate in multisig wallets, with other signers: Require M of N signature to approve funds moving.
-
Sign text messages to prove control over private key.
Available For Pre-Order
Limited quantity of the first batch pre-orders of Mk3 is opening today, and these units are planned to ship by October 2019.
Enjoy the early-bird prices!
We reserve the right to change the features and prices at anytime without notice.
Bulk orders
If you are already a Opendime reseller or NEW and interested in reselling, reach out to support for orders over 50 quantity.
Podcaster?
We now have referrals and promo-codes, contact support for more information.
F.A.Q
Q: I’ve got a Mk2 and want to switch to Mk3. How?
A: Using a micro SD card, perform an encrypted backup and then restore it onto your new Mk3.
Destroy your old Mk2 or keep it secure as hot backup.